Cyber insurers have changed the rules and most IT teams haven’t caught up. If your organization still relies on VPN-based perimeter access, flat network architecture, or implicit trust between users and resources, you are carrying risk that cyber insurance underwriters are actively refusing to cover. This isn’t a theoretical future problem. In 2025 and into 2026, carriers are issuing coverage denials, adding exclusion clauses, and substantially increasing premiums for organizations that cannot demonstrate identity-based access controls, enforced multi-factor authentication (MFA), and device compliance verification.
The core issue is simple: cyber insurance exists to transfer financial risk. Underwriters will only accept that transfer when they can verify that your controls actually reduce the probability and severity of a breach. Traditional network access models —VPNs, castle-and-moat perimeters, implicit internal trust—do not provide that assurance. They never did. Now, after several years of high-profile ransomware and supply chain attacks, insurers know it.
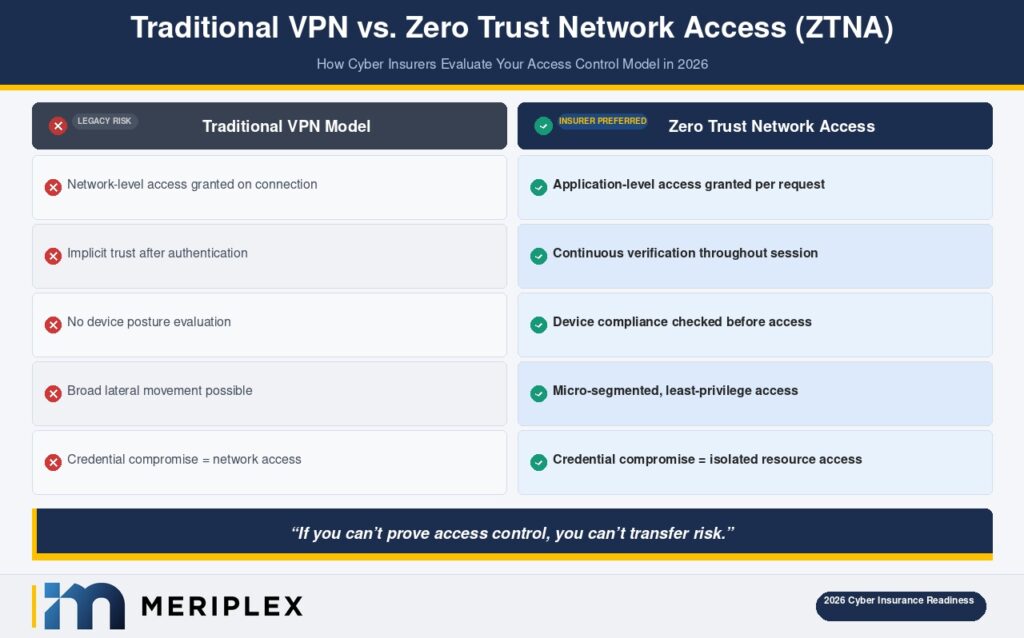
If you can’t prove access control, you can’t transfer risk. This post explains what the underwriting shift means, what insurers are specifically looking for, and how Zero Trust Network Access (ZTNA) serves as the compensating control that changes the conversation.
The Underwriting Shift Is Already Underway
Cyber insurance is no longer the flexible safety net it was five years ago. According to data from Marsh’s 2024 Global Insurance Market Index, cyber premium rates surged dramatically in prior years, and while rate increases have stabilized in some segments, coverage restrictions have tightened considerably. Underwriters have responded to a claims environment defined by ransomware, business email compromise, and third-party vendor breaches by building more rigorous control requirements directly into policy language.
What this looks like in practice: organizations applying for or renewing cyber coverage are now required to complete detailed security questionnaires that go far beyond checkbox compliance. These questionnaires—from carriers including Chubb, AXA XL, Coalition, and others—explicitly ask about MFA coverage across all remote access, admin account protections, privileged access management (PAM), endpoint detection and response (EDR), and increasingly, whether network access is governed by identity and device posture rather than IP address or VPN connection.
The consequences for organizations that answer “no” or “partial” are immediate: higher premiums, sub-limits on ransomware coverage, co-insurance requirements, or outright denial.
The Verizon 2024 Data Breach Investigations Report found that stolen credentials remained the top attack vector, involved in over 77% of web application breaches. Insurers read that report. When your access model relies on username-and-password VPN credentials as the primary perimeter control, you are presenting an insurer with exactly the attack profile they are trying to avoid insuring.
Your Renewal Window Is Shorter Than You Think
What "Traditional Network Access" Actually Means and Why It's a Liability
Traditional network access refers to architectures built on the assumption that the corporate network perimeter is a trustworthy boundary. Once inside — through a physical office connection, a site-to-site VPN, or a remote VPN tunnel — users and devices are implicitly trusted and can move laterally across the network with minimal friction.
This model has three fundamental problems that underwriters now penalize:
Implicit trust creates uncontrollable blast radius. When a threat actor compromises a single VPN credential, they gain a foothold inside the network with broad lateral movement potential. The 2021 Colonial Pipeline attack, the 2023 MOVEit vulnerability exploitation, and countless ransomware incidents all exploited this dynamic. A compromised endpoint becomes a launching point rather than an isolated failure.
VPNs provide access, not verification. A VPN confirms that a user has valid credentials and a functioning tunnel. It does not verify whether that user is who they claim to be, whether their device is patched and compliant, or whether they should have access to the specific resources they’re reaching. Underwriters are keenly aware that “connected to the network” and “authorized for this resource” are not the same thing.
Flat network architecture amplifies every compromise. When systems, applications, and data are not segmented by function or sensitivity, a breach in one area propagates freely. This is what turns a contained incident into a catastrophic ransomware event that encrypts an entire environment — the scenario insurers pay out on most often, and the one they are most aggressively trying to price and restrict.
In our experience working with mid-market organizations across healthcare, financial services, and oil and gas, the perimeter model often exists not by design but by inertia. It was what worked when everyone was in the office and the threat landscape was different. That’s no longer the environment any organization operates in.
What Insurers Are Actually Looking For: The Language That Matters
Cyber underwriters are not evaluating your general security posture. They are looking for specific, verifiable controls. Understanding their language is the first step to meeting their requirements.
Identity-Based Access Control
Insurers want evidence that access to resources is determined by verified identity, not network location. This means access policies that tie permissions to a specific authenticated user identity rather than to “anyone on the corporate network” or “anyone connected via VPN.” Directory integration (Active Directory, Azure AD/Entra ID), role-based access control (RBAC), and just-in-time (JIT) access provisioning all support this posture.
MFA Enforcement—Across All Remote and Privileged Access
MFA is no longer optional on cyber applications—it is a baseline requirement. But carriers are now asking the harder follow-up questions: Is MFA enforced on all remote access pathways, including service accounts and administrative interfaces? Is it phishing-resistant (FIDO2/WebAuthn) or legacy SMS-based? Is there MFA bypass risk through legacy authentication protocols?
Organizations with incomplete MFA coverage—particularly around privileged accounts and legacy apps—consistently see this reflected in policy sub-limits or exclusions.
Access Control Modernization Isn't Just a Security Project—It's a Coverage Decision
Device Compliance Verification
Access from an unmanaged, unpatched, or compromised device is a major underwriting concern. Insurers look for evidence that your access infrastructure can evaluate the posture of a connecting device—Is it enrolled in MDM? Is it patched to a current OS level? Does it have active EDR?—and can deny or limit access when a device fails compliance checks. This is often called device trust or device posture assessment.
Network Segmentation
Can you demonstrate that a breach in one environment—say, a contractor’s workstation or a development server—cannot propagate freely into production systems or high-value data stores? Micro-segmentation, application-layer segmentation, and east-west traffic controls are all evidence underwriters seek.
ZTNA as the Compensating Control That Changes the Conversation
Zero Trust Network Access (ZTNA) is the architectural framework that directly addresses each of these underwriting requirements. ZTNA operates on the principle of “never trust, always verify”—access to any resource is evaluated continuously based on user identity, device posture, behavioral context, and explicit policy, regardless of where the user is located.
Where a VPN grants broad network access, ZTNA grants access to a specific application or resource only—and only after verifying that the user and device meet defined conditions at the time of each request.
This matters to insurers for a concrete reason: ZTNA dramatically reduces blast radius. If a credential is compromised, the attacker gains access only to the specific resource that credential is permitted to reach—not the entire network. Combined with strong MFA enforcement and continuous device posture checks, ZTNA turns a potential catastrophic breach into a contained incident.
The language translates directly to underwriting requirements:
At Meriplex, when we help clients prepare for cyber insurance renewal or initial application, ZTNA implementation is consistently among the highest-leverage steps they can take—both for measurable risk reduction and for the ability to document controls that satisfy underwriter requirements.
ZTNA platforms—including Zscaler Private Access, Palo Alto Prisma Access, Microsoft Entra Private Access, and others—are now well-integrated with enterprise identity providers and endpoint management tools. This is not an aspirational architecture. It is a deployable solution that mid-market organizations can implement in phased approaches aligned to their renewal timelines.
See Exactly Where Your Access Controls Fall Short—Before Your Insurer Does
What This Means for Your Business
The shift in cyber insurance underwriting is not a temporary market correction. It reflects a permanent recalibration of how risk is assessed when networks are defined by identity rather than perimeter.
For IT directors and CISOs evaluating their posture heading into 2026, the practical takeaways are direct:
Audit your access model before your insurer does. If you’re operating on a VPN-first architecture with limited MFA enforcement or no device posture checks, assume your next renewal conversation will be difficult. Run that gap analysis now while you have time to address findings.
Document your controls explicitly. Insurers cannot credit controls they can’t see. Maintaining clear records of your MFA deployment coverage, ZTNA policy framework, device compliance enforcement, and privileged access management gives your broker the evidence needed to negotiate on your behalf.
Treat ZTNA adoption as a business continuity investment, not just a security project. The ROI is measurable: reduced breach exposure, preserved insurability, and in many cases, premium reduction from carriers who reward organizations demonstrating mature access controls.
Work with a managed security partner who understands both the technical and insurance dimensions. The intersection of security architecture and insurance requirements is a specialized space. Meriplex’s security team works with clients across healthcare, financial services, oil and gas, and other sectors to align their access controls with current underwriting expectations — not just current threat intelligence.
Frequently Asked Questions
Why is cyber insurance getting harder to qualify for?
Cyber insurers have sustained significant losses from ransomware, business email compromise, and supply chain attacks over the past several years. In response, they have tightened underwriting requirements to ensure organizations carry meaningful preventive controls before coverage is issued. Organizations that cannot demonstrate identity-based access control, enforced MFA, and network segmentation are now frequently denied coverage or offered policies with restrictive sub-limits and exclusions.
What is ZTNA and how does it differ from a VPN?
Zero Trust Network Access (ZTNA) is a security framework that grants access to specific applications or resources based on continuous verification of user identity, device posture, and access policy — rather than connecting a user to the broad corporate network. A VPN provides network-level access after a single authentication event and does not evaluate device health or enforce least-privilege access. ZTNA eliminates implicit trust and dramatically reduces lateral movement risk in the event of a credential compromise.
What access controls do cyber insurers specifically require in 2026?
Most carriers now require: multi-factor authentication enforced across all remote access and privileged accounts; identity-based access policies rather than IP- or VPN-based access; device compliance verification (patching, MDM enrollment, EDR presence) as a condition of access; privileged access management (PAM) for administrative credentials; and evidence of network segmentation that limits lateral movement. Requirements vary by carrier and coverage tier, but these represent the consistent baseline across the market.
Can implementing ZTNA lower my cyber insurance premiums?
Yes, in many cases. Carriers including Coalition, Cowbell, and others explicitly reward organizations with mature access control frameworks — including ZTNA adoption, phishing-resistant MFA, and endpoint compliance enforcement — with better coverage terms and lower premiums. The key is being able to document your controls clearly during the application and renewal process. A managed security provider can help you build that evidence package.
What should I do if my cyber insurance application was denied due to access control gaps?
First, request specific detail on which controls were cited as insufficient — this is your remediation roadmap. Common gaps include incomplete MFA coverage, legacy VPN reliance without device posture checks, and unmanaged privileged accounts. Work with a security partner to address the highest-priority findings, document your progress, and reapproach carriers with a written security improvement plan. Many carriers will re-engage when they see credible, in-progress remediation.
The Bottom Line
Cyber insurance underwriters are not creating new rules arbitrarily. They are pricing risk based on what the claims data tells them: organizations relying on traditional perimeter access models are materially more likely to experience severe, costly incidents. The controls they require—identity-based access, MFA enforcement, device compliance, network segmentation—exist in the market today, are implementable at mid-market scale, and deliver security value independent of what they do for your insurance profile.
The organizations that will maintain favorable coverage terms through 2026 and beyond are the ones treating access control modernization as a business-critical initiative, not a future-state aspiration.



